Yugabyte Partners with HashiCorp Vault for Centralized Secrets Management
Yugabyte is on a mission to build the leading distributed database for cloud native applications and simplify operational data infrastructure. The Yugabyte team is delighted to announce a new technology partnership with HashiCorp, a market leader in multi-cloud infrastructure automation software. The partnership brings integration of Yugabyte Platform with HashiCorp Vault.
The Yugabyte Platform integration is officially verified and approved by HashiCorp. This enables you to manage and control access for encryption keys, TLS certificates, and database users programmatically in HashiCorp Vault.
Benefits of integrations
Specifically, the expanded partnership between Yugabyte and HashiCorp delivers some key benefits:
- Simplify secrets management: Generate and manage secrets for YugabyteDB database users, encryption keys, and TLS certificates with HashiCorp Vault.
- Safely automate dynamic secrets delivery: Dynamic generation of secrets allows us to manage intentions instead of managing credentials, by creating a moving target for attackers and minimizing the risk of exposing credentials.
- Cloud-first and platform agnostic: HashiCorp Vault and Yugabyte Platform make it easy to programmatically manage secrets across cloud providers and platforms.
- Standardize and control workflows: Provides consistent workflow for distribution and lifecycle management of cryptographic keys in various key management service (KMS) providers. It also automates certificate lifecycle (lease, renew, revoke) management.
What is Yugabyte Platform?
Yugabyte Platform includes a powerful graphical user interface for managing fleets of database clusters deployed across zones, regions, and clouds from one place. It also takes the 100% open source YugabyteDB to the next level for enterprise productions. Yugabyte’s users rely on the Platform Console to deliver YugabyteDB as a private DBaaS through streamlined operations and consolidated monitoring.
What is HashiCorp Vault?
HashiCorp Vault provides the foundation for modern multi-cloud security. It was purpose-built in the cloud era to authenticate and access different clouds, systems, and endpoints, and centrally store, access, and deploy secrets (API keys, credentials, etc.). It also provides a simple workflow to encrypt data in flight and at rest
Vault has a free, open source offering as well as an enterprise version, which includes advanced features to support collaboration, governance, and multiple datacenters. However, Vault offers integrations with many popular identity providers, including cloud IAM platforms, Kubernetes, and Active Directory. It also supports both public clouds and private datacenters with a broad range of endpoint systems, including databases, cloud platforms, messaging queues, SSH, and more.
Let us go through the above mentioned integration benefits in detail.
Manage YugabyteDB encryption keys with HashiCorp Vault
Organizations need a consistent workflow for distribution and lifecycle management of cryptographic keys in various key management service (KMS) providers. It allows organizations to maintain centralized control of their keys in Vault while still taking advantage of cryptographic capabilities native to the KMS providers.
There are two types of keys to encrypt data in YugabyteDB:
- Universe key: Top level symmetric key used to encrypt other keys (see data keys below), these are common to the cluster.
- Data key: Symmetric key used to encrypt the data. There is one data key generated per flushed file.
For each universe (or cluster), there is a top level universe key that encrypts a group of data keys. The data keys are responsible for encrypting the actual data. The user controls the universe keys, while data keys are internal to the database. But encryption at rest uses universe keys to encrypt and decrypt universe data keys.
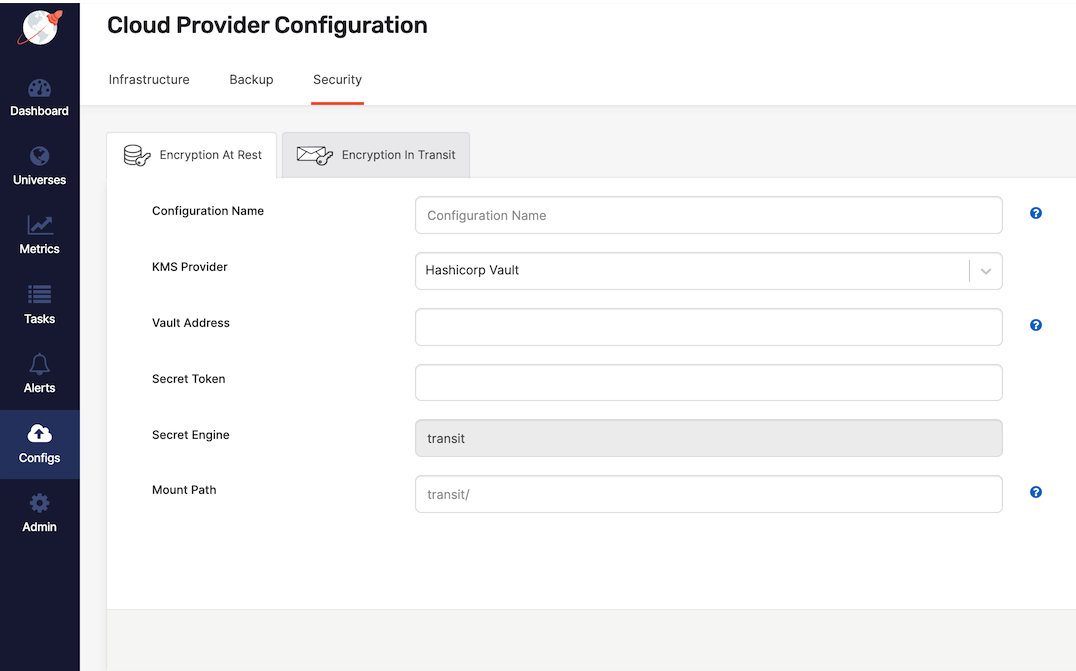
However, you can use the Yugabyte Platform to create KMS configurations for generating the required universe keys for one or more YugabyteDB universes. Encryption at rest in Yugabyte Platform supports the use of HashiCorp Vault as a KMS. You can follow this link for how to configure HashiCorp Vault as a KMS provider for Yugabyte Platform. In addition to secret token based access for dev/testing environments, users can configure TLS based or IAM based access mandated for production environments.
Automate certificate lifecycle management for YugabyteDB using HashiCorp Vault
Certificates are at the nexus of modern, secure communication. One of the challenges many enterprises face today is keeping track of various certificates. Another challenge is ensuring those certificates associated with critical applications deployed across multi-cloud are current and valid.
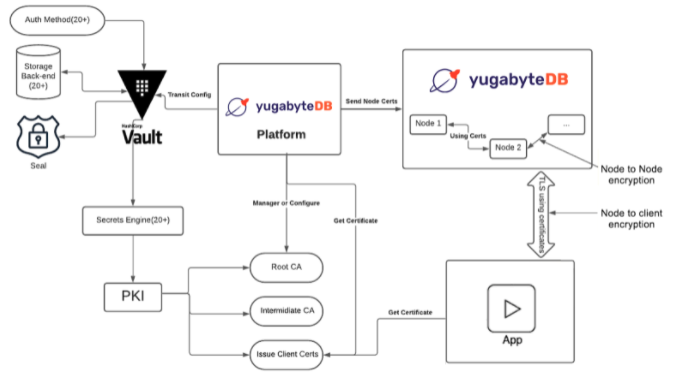
All Yugabyte products use TLS 1.2 for communicating with clusters, and digital certificates to verify the identity of clusters. Using TLS with a digital certificate encrypts the data in transit to ensure a secure connection to your cluster. It also prevents man in the middle (MITM) attacks, impersonation attacks, and eavesdropping.
Yugabyte Platform allows you to protect data in transit by using the following:
- Server-to-server encryption for intra-node communication between YB-Master and YB-TServer nodes.
- Client-to-server encryption for communication between clients and nodes when using CLIs, tools, and APIs for YSQL and YCQL.
Yugabyte Platform lets you create a new self-signed certificate, use an existing self-signed certificate, or upload a third-party certificate from external providers.
Safely automate dynamic secrets delivery
Data protection is a top priority, and database credential rotation is a critical part of any data protection initiative. When a system is attacked by hackers, continuous credential rotation becomes necessary and needs to be automated.
Use of dynamic secrets allows us to manage intentions (e.g., web server needs database access) instead of managing credentials (e.g., authentication data provided to web servers requiring database access). This allows us to achieve the same end goal while solving major challenges, including leaky applications, non-repudiation, automatic rotation, and practical revocation. See Why We Need Dynamic Secrets for more details.
Vault’s database secrets engine generates database credentials dynamically based on user-defined roles. The database administrator can pre-define the time-to-live (TTL) of the database credentials to enforce its validity. This ensures they are automatically revoked when they expire.
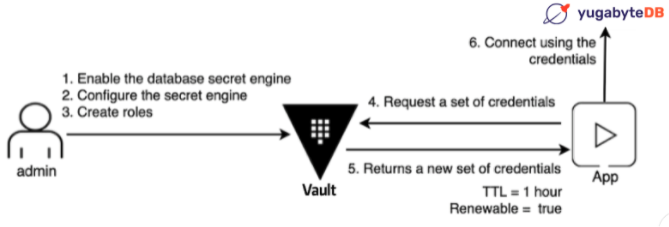
Each app instance can get unique credentials that they don’t have to share. By making those credentials short-lived, you reduce the chance that they might be compromised. If an app was compromised, the credentials used by the app can be revoked rather than changing more global sets of credentials.
Vault Plugin for YugabyteDB project implements Vault’s Custom Database plugin interface for providing support for creating dynamic credentials in YugabyteDB. Please follow the instructions on how to configure and use this integration.
Vault storage backend using YugabyteDB
The YugabyteDB storage backend is used to persist Vault’s data in a YugabyteDB cluster. YugabyteDB is compatible with the PostgreSQL database driver and uses that driver to interact with the database. Currently, the community supported YugabyteDB storage backend does not support high availability.
Summary
Yugabyte and HashiCorp offer a common blueprint for simplifying secrets management, safely automating dynamic secrets delivery, and controlling standardized workflows in multi-cloud environments adaptable to the needs of any enterprise. With our cloud-first and platform-agnostic approach, HashiCorp Vault and Yugabyte Platform make it easy to programmatically manage secrets across cloud providers and platforms.
Finally, we’re excited about the benefits this partnership will deliver to our joint customers. We look forward to continued work with HashiCorp to deliver best-in-class solutions for our joint customers.